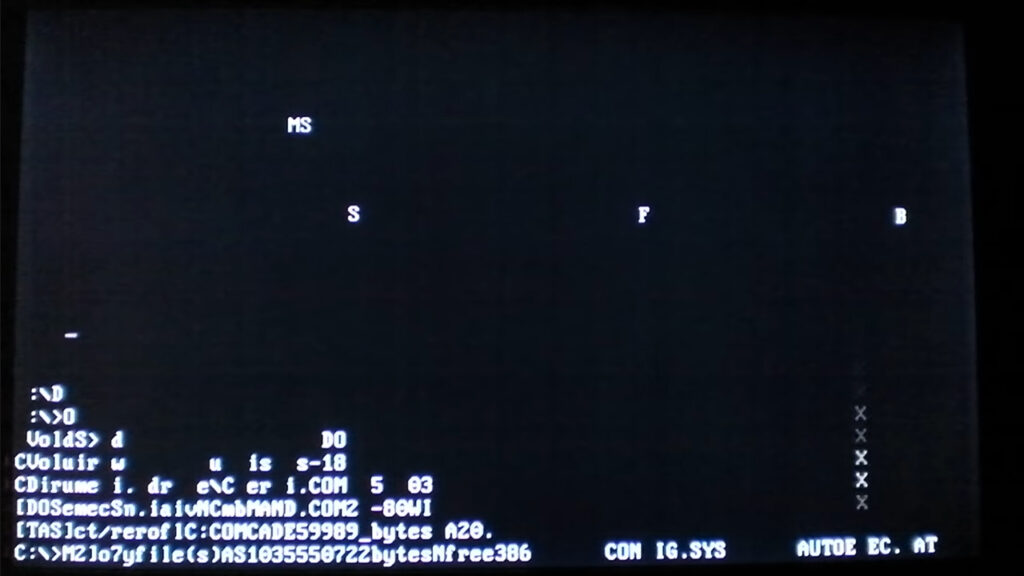
The year is 1990. I’m sitting in front of my CRT, and my computer is running WordPerfect and MS-DOS. I’m working on a school assignment for my senior year, and just like the students today, I waited until last minute to start. My typing skills are lacking, and it takes me a long time to finish. With just a few hours before the assignment is due, I finally key in the last words.
I’m getting ready to print the assignment when suddenly a letter falls to the bottom of my screen. Am I getting tired from staring at a CRT monitor for too long? I rub my eyes to clear my vision, then try again to send the document to the printer.
Too much screen time?
But another character falls, followed by a third. One by one, all the characters fall from the screen and create a pile of jumbled letters at the bottom. All I can do is watch the rain of letters, accumulating at the bottom of my screen. I clear the screen and reopen my document. But after a few seconds, the letters start falling again.
I had become a victim of the Cascade virus.
A fun, childish prank?
The first generation of viruses were the equivalent of childish pranks. Sometimes they were even fun to see in action. But since the days of Cascade, viruses have evolved. What was called a virus has evolved into its own category of software, termed malware. And malware is no joke.
Today malware is smarter. Malware programs are designed to destroy systems, cause chaos, steal sensitive information, perform corporate espionage, install ransomware and steal identities. Malware can also be used for cyberwarfare and cryptomining. The developers of such malicious programs write more and more complicated algorithms, making the malware harder to detect and sometimes impossible to remove.
How do you avoid becoming a victim of malicious code?
Protect, prevent and scan
Install a malware and virus detection suite
These days most operating systems come with built-in virus scanning. For more advanced virus and malware protection, you can take your pick from a number of reputable providers. Malwarebytes, Norton, Webroot and Eset all provide good solutions.
Keep your chosen malware software updated
Hackers are discovering new vulnerabilities and writing new code to exploit those vulnerabilities all the time. So your anti-virus/anti-malware program will be useless if you don’t make sure it has the most recent updates.
Do not open suspicious emails or attachments
The number one medium for virus and malware infection is email. Think twice before clicking links in email messages. And review any email with an attachment, to stop email attacks in their tracks.
Avoid software from suspicious origins
Downloaded a program from the internet? Which site did it come from? Did you ask for it specifically, or was it something you clicked on because a webpage said your computer was running slow? Delete it! If in doubt, you can scan a downloaded file with Virus Total.
Install a browser plugin
Firefox and Google Chrome will automatically scan sites and incoming downloads for known malware. For additional protection, you can install a browser plugin like uBlock Origin. Set uBlock to filter all connections to malware domains, cryptomining and “malvertising” sites.
Change your DNS provider
Another line of defense in the war against malware… On your home or office router, change the default DNS provider from your service provider. Use a provider such as OpenDNS, Quad9 or Cloudflare that will block connections to known malware sites.
Conclusion
Have you been pranked by malicious software like the Cascade virus? While it might be amusing, this “malware story” is a reminder that your data is under attack all the time.
Keep yourself educated on the latest security threats and follow the tips here to secure your computer, your email and your browsing online. Protect, prevent and scan! Read more to stay updated on the newest threats and malware trends.
Improve the cybersecurity stance for your business and your personal data. And follow this simple tip for safer computing.




2 Responses
Thanks for another educational post. Having to work from home at this time it’s been great to learn about cybersecurity, virtual meeting platforms and avoiding ransomware “invitations”.
Very entertaining!
Learned something new while laughing at the story,
Great article, cant wait for more to come….